At GitLab, we’re all about iteration. It helps us continuously push out product improvements and additional value to our users. One interesting side effect of iteration is that it can make it harder to see the true scope of what you’ve delivered. Rather than a few big bang giant feature releases per year, a steady flow of iterative improvements requires taking a few steps back to look at all the work in aggregate to get a full sense of accomplishment. As we look forward to 2021, it’s worth a look back to see how far the Threat Insights group has come with Vulnerability Management in the past year.
The year 2020 was filled with unprecedented challenges far beyond what most of us have ever experienced. The Threat Insights team formed against a backdrop of uncertainty with a global pandemic just starting to spread. Most of our team joined GitLab last year. We took over a fledgling area of the product that was off to a good start but hadn’t had a dedicated team to push it forward. Many of us—myself included—had security experience yet little to no background in vulnerability management. In short: we faced a daunting challenge.
Initially, progress was slow as we took inventory of the current state of Vulnerability Management. We gathered input from others who worked on existing functionality. Early on, we determined that a major architectural upgrade to how GitLab stored vulnerability data from pipeline jobs was essential to do first. It took several months of hard work that culminated in Standalone Vulnerability Objects debuting in GitLab 13.0 in May.
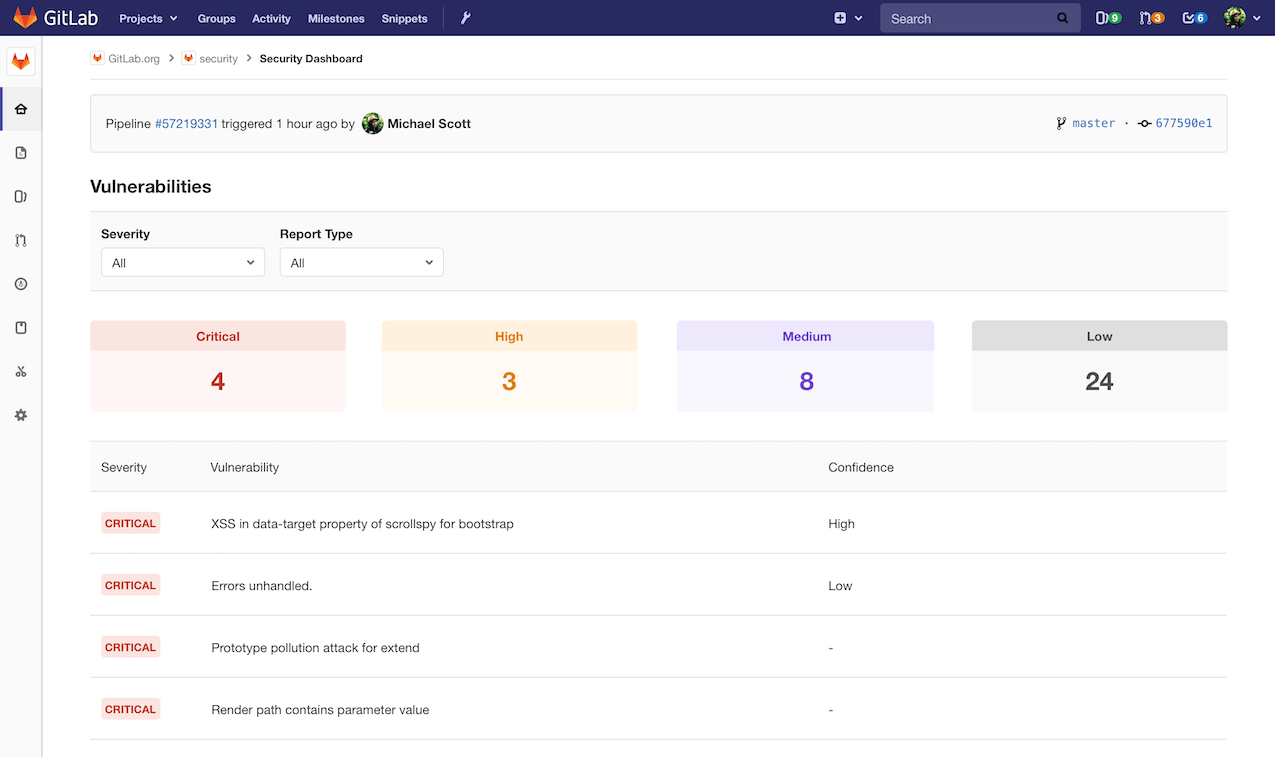 Project-level Vulnerability Management in early 2020
Project-level Vulnerability Management in early 2020
You may be wondering how a post that started by talking about iteration fits with spending a few months for one big change. Sometimes there are necessary exceptions where iterative releases would be more disruptive to users. Because we were changing the underlying storage model for vulnerability data, it was critical to upgrade all components of Vulnerability Management together. Otherwise, the experience for our users would have been inconsistent and confusing. We did still develop the new vulnerability object model iteratively; however, the work was held back behind a (large) feature flag until all pieces were complete and we could publicly release them simultaneously.
The Standalone Vulnerability Objects release was a major step forward technically. It also brought about another key milestone: Vulnerability Management’s maturity officially moved to Minimal. Reaching Minimal signaled our category now had a complete foundation on which our users could build their vulnerability management and remediation programs. Getting this key piece of architecture in place further marked a turning point in our team’s ability to start quickly delivering new features built on top of it.
To illustrate how much the team accomplished just since 13.0, here are some highlights from our May-December progress:
- 10 release post-worthy new features
- Over 40 total new features and enhancements to existing features
- Numerous new GraphQL endpoints (and one of the first teams to go GraphQL-first)
- Over 150 bugs squashed
- Numerous technical and performance improvements
We transformed the Group- and Project-level Security Dashboards into separate experiences for dashboarding and working with vulnerability lists. We created a personal Security Center. We made managing vulnerabilities a more seamless part of an integrated DevSecOps workflow with new features like linking existing issues to vulnerabilities, showing pipeline status on Project Security Dashboards, and adding Special references for vulnerabilities. And, perhaps most impressively, Vulnerability Management reached the next maturity level of Viable a mere 7 months after reaching Minimal—and a month ahead of plan. Reaching Viable so quickly is an especially big achievement since it requires successfully passing a research-based maturity evaluation process with real users.
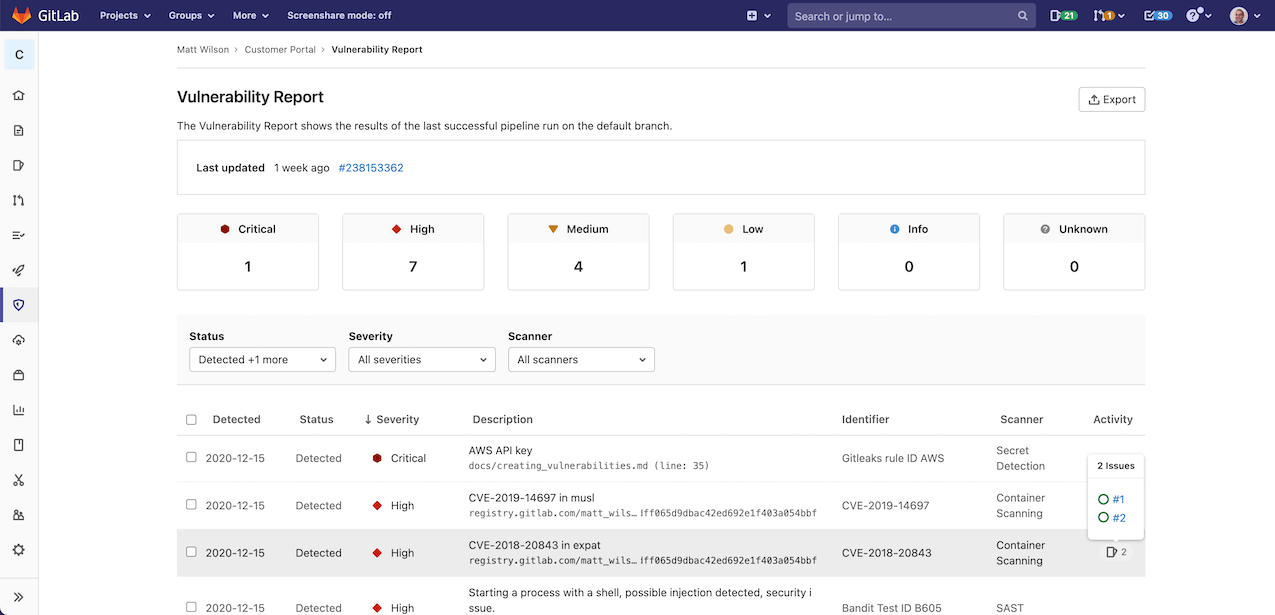 Project-level Vulnerability Management in December 2020
Project-level Vulnerability Management in December 2020
Last year, many of us were stuck at home, our routines becoming monotonous with days seeming to blur together. It’s easy to get lost in the day-to-day. This can make it difficult to see just how much forward progress might actually be happening. Taking time to inventory our accomplishments highlights that we achieved quite a bit in a few short months. This perspective of hindsight makes it clear just how far we’ve come. None of this would have been possible without hard work and dedication by the talented Threat Insights team. As we look forward to 2021, I’m excited about what lies ahead. Expect even more big things—in monthly iterations—from Threat Insights!
Cover image by Marcello Gennari on Unsplash

