API development is all the rage these days for customer and partner integration, frontend-to-backend communication, microservices orchestration, and more. Yet APIs have their challenges, including how to create a fast feedback loop on design, how different teams can work with autonomy without having to wait for each other's API implementation, and how to cope with backward compatibility tests when shipping newer versions of the API.
Microcks, an open source, Kubernetes-native tool for API mocking and testing, addresses these challenges. With Microcks, which is accepted as a Sandbox project in the Cloud Native Computing Foundation, developers can leverage their OpenAPI, GraphQL, gRPC, AsyncAPI, and Postman Collection assets to quickly mock and simulate APIs before writing them. Couple Microcks with GitLab and you have a powerful combination to foster collaboration, encourage rapid changes, and provide a robust delivery platform for API-based applications.
In this ongoing blog series, we will introduce you to Microcks use cases and how they fit with the GitLab platform. We'll also discuss technical integration points that will help ease the developer burden, including identity management, Git repositories, and pipeline integrations.
What is Microcks?
Microcks addresses two major use cases:
- Simulating (or mocking) an API or a microservice from a set of descriptive assets. This can be done as soon as you start the design phase to set up a feedback loop very quickly, or later on to ease the pain of provisioning environments with a lot of dependencies.
- Validating the conformance of your application regarding your API specification by running contract-test. This validation can be integrated into your CI/CD pipeline so that conformance can be checked on each and every iteration. This is of great help to enforce backward compatibility of your API of microservices interfaces.
Microcks offers a uniform and consistent approach for the various kinds of request/response APIs (REST, GraphQL, gRPC, Soap) and event-driven APIs (currently supporting eight different protocols), thereby bringing consistency for users and for automations all along your API lifecycle.
How Microcks fits into the software development lifecycle
Microcks is a solution based on containers and can be deployed in several configurations. It can be deployed on the developer laptop through Docker, Podman or Docker Desktop Extension to assist with mocking complex environments. When it comes to team collaboration, Microcks can be deployed as a centralized instance that connects to the Git repositories of the organization, discovers the API artifacts, and then provides shared up-to-date API simulations.
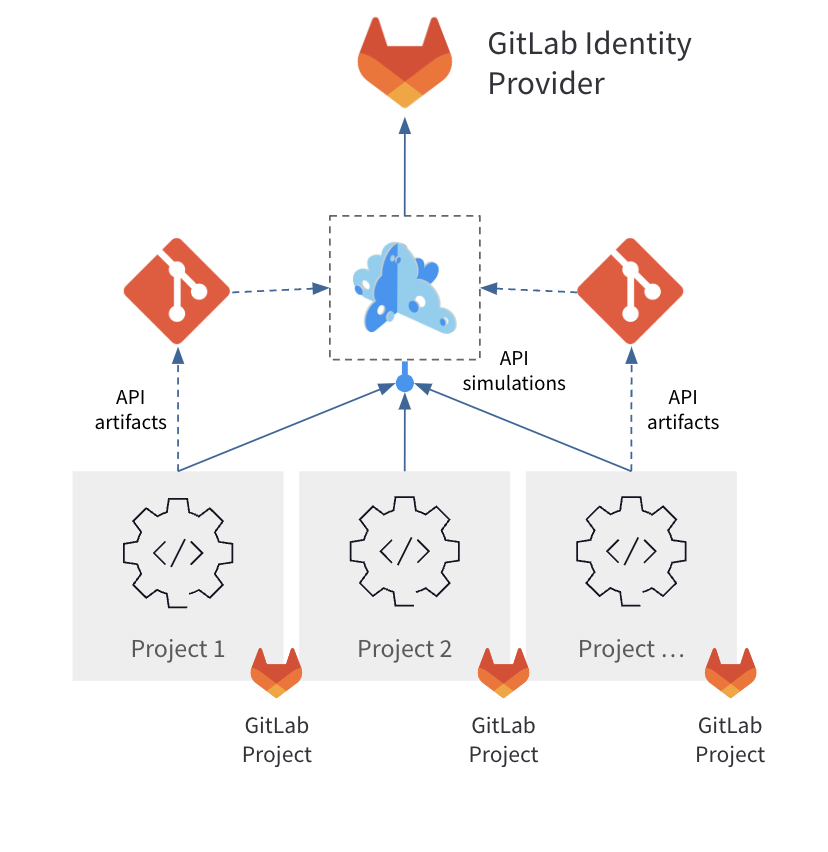
To ease the burden on developers (and administrators), Microcks can be configured to use your GitLab platform as an identity provider. With that configuration, integrating Microcks is seamless, and API simulations are automatically shared among development teams. Microcks fosters collaboration by providing everyone with the same “source of truth” and avoiding drift risks. The tool can also be used to lower the pain and the cost of deploying and maintaining complex QA environments because simulations are inexpensive to deploy or redeploy on-demand. Microcks deployment follows a GitOps approach.
Beyond this sharing of simulations, Microcks also integrates well with CI/CD pipelines. As you release API-based applications, there is always concern about conformance of the contractualized expectations you defined using specifications like OpenAPI, GraphQL, and the like. Usually, the hardest part isn't delivering the 1.0 of this API; problems come later when you're trying to deliver the 1.3. This latest version must still be backward compatible with the 1.0 contract if you don't want to make your consumers angry and frustrated.
This conformance validation is very well assured by Microcks using contract-testing principles. So we encourage you to plug Microcks into some test related jobs in your GitLab pipeline and delegate this conformance validation to your Microcks instance.
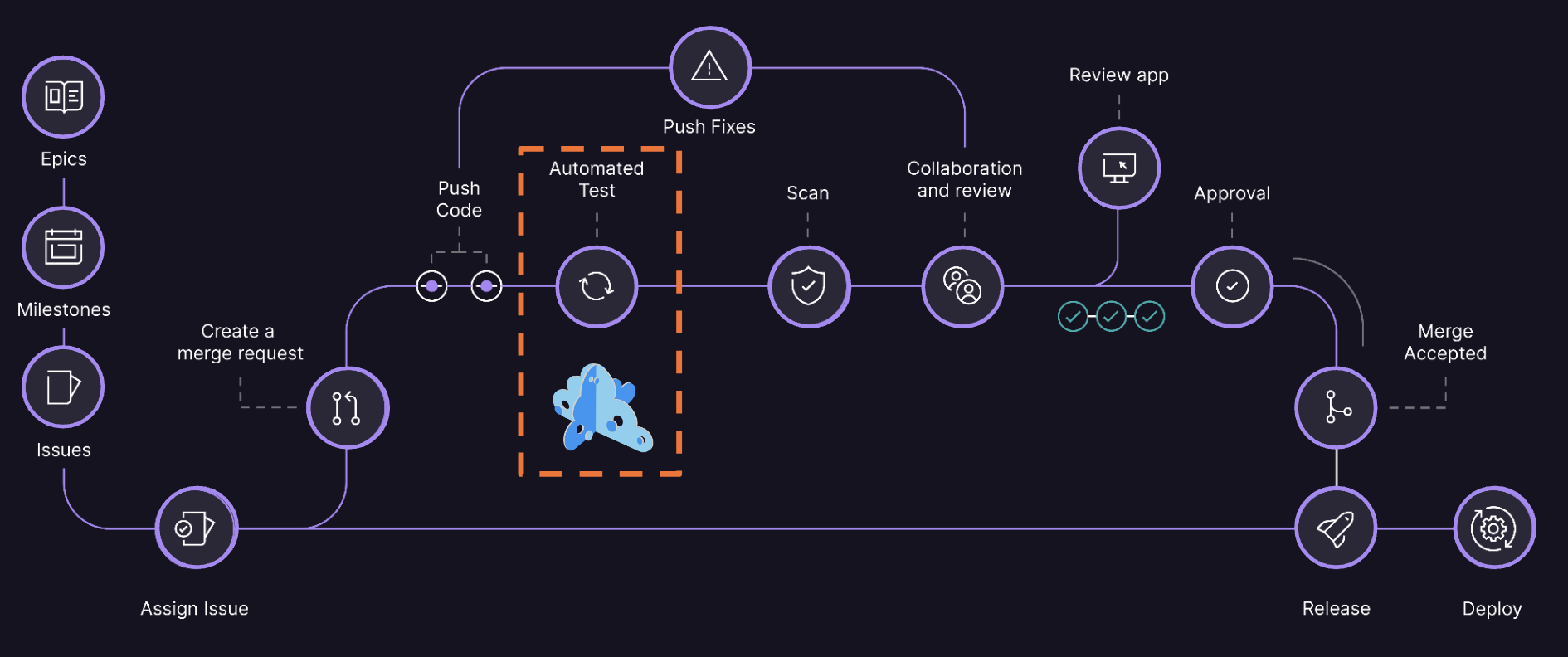
Embedding Microcks conformance testing in your pipeline is actually easy thanks to our lightweight CLI that you'll integrate in pipeline jobs. You can choose to reuse an existing Microcks instance to record results and keep history of your success or pop up a new ephemeral instance as it's lightweight and fast to bootstrap.
How to set up GitLab as an identity provider in Microcks
To start off this series, we will detail how to configure Microcks to use your GitLab platform as an identity provider. This is in fact very easy as authentication in Microcks is based on Keycloak (another CNCF project) and GitLab can be set as an identity provider in Keycloak (see official documentation).
Note: This configuration is optional as Microcks can use any other identity provider Keycloak integrates with.
Keycloak is a very common solution that may be deployed already at your organization. If not, Microcks comes with a Keycloak distribution that is pre-configured for its usage with a realm called microcks. We have used this realm to validate this configuration.
Create a GitLab Group Application
The first thing is to create a new Group Application on your GitLab instance as follows:
Name:microcks-via-keycloakRedirect URI:https://keycloak.acme.org/realms/microcks/broker/gitlab/endpointScopes:read_user,openid,profileandemail
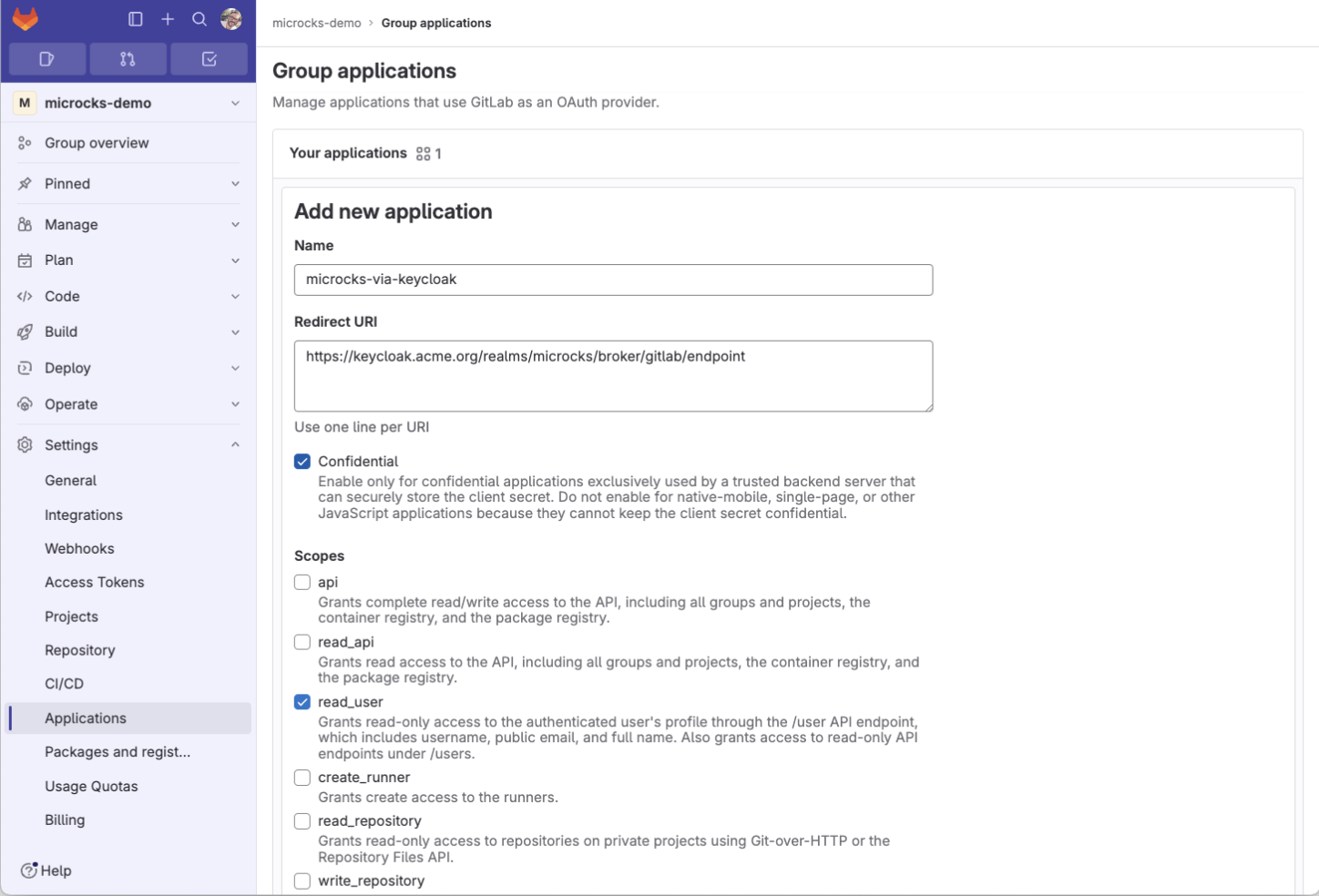
This application uses your Keycloak instance with https://keycloak.acme.org/realms/microcks/broker/gitlab/endpoint as the redirect URI. As a result, we obtain an Application ID and an associated Secret we have to keep aside for the next step.
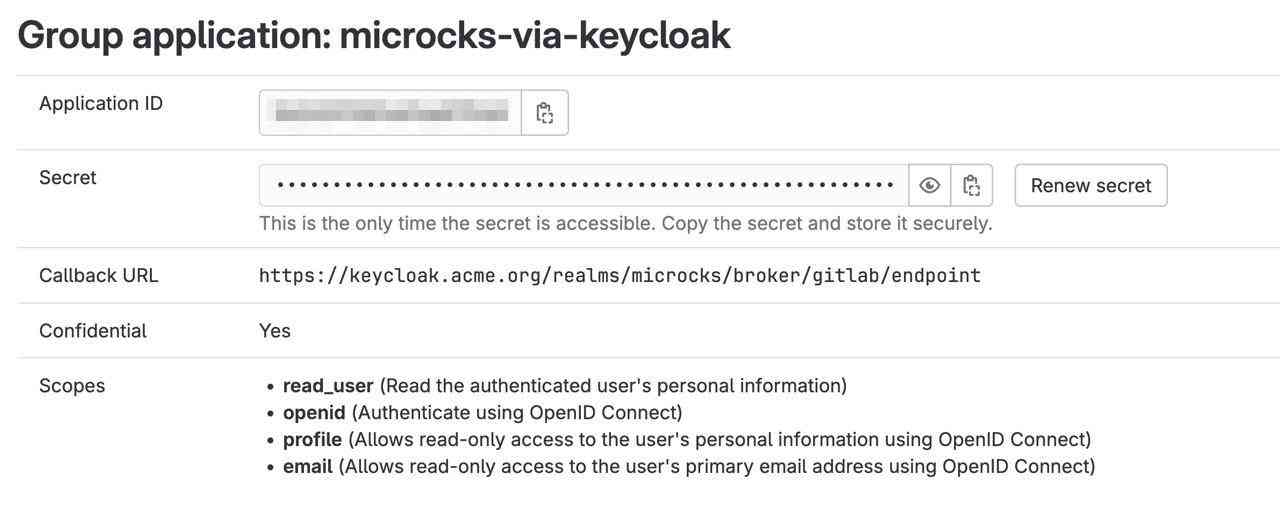
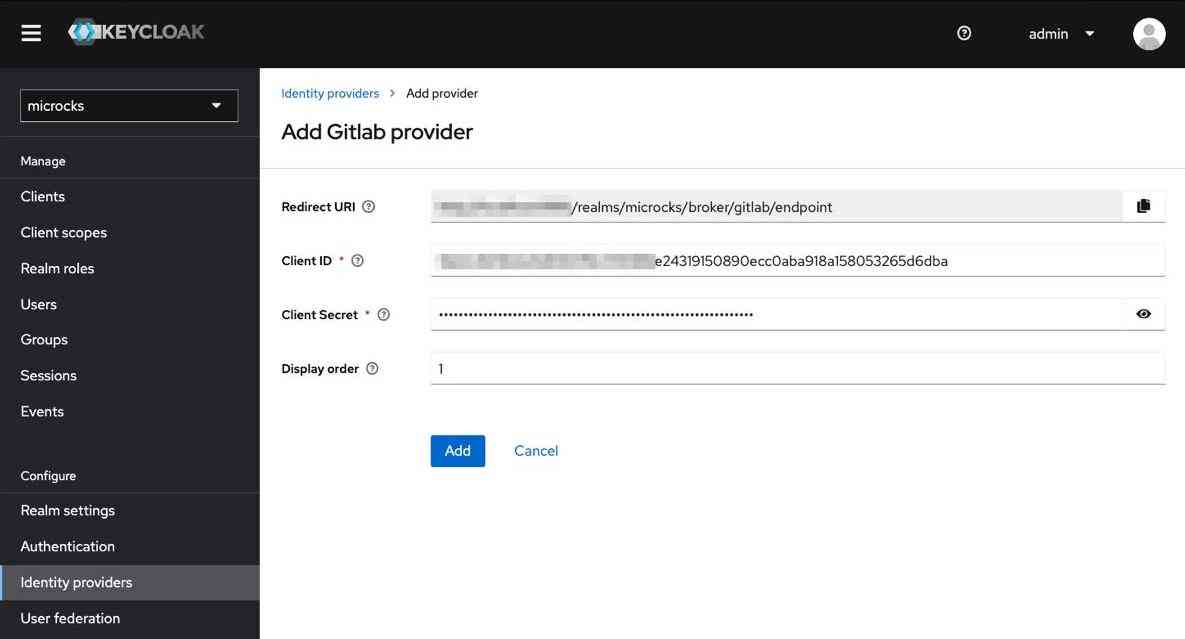
Add GitLab as identity provider in Keycloak
The next step takes place in the Keycloak admin console. Once the correct microcks realm is selected, you'll just have to go to the Identity providers section and add a GitLab provider. Simply paste here the Application ID you got earlier as Client ID and the Secret as Client Secret. You can also choose a Display order if you plan to have multiple identity providers.
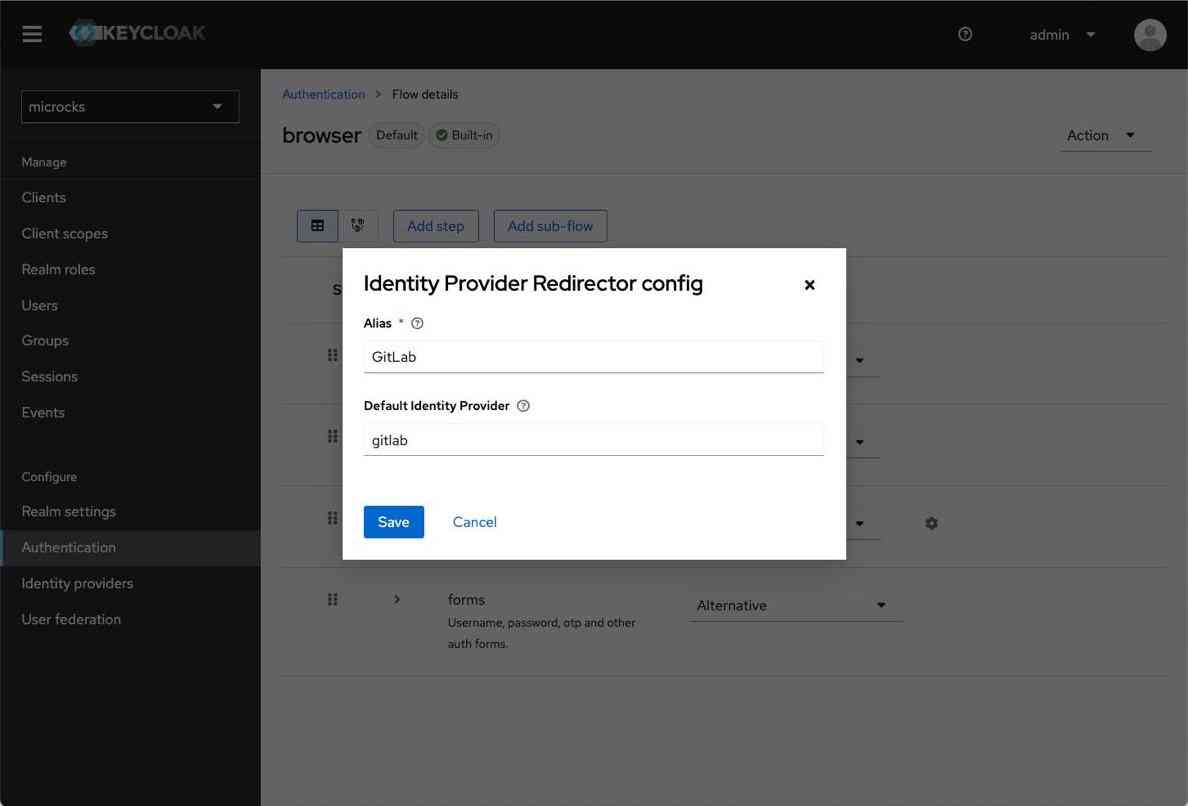
Then, from the Authentication section in the admin console, choose the browser flow and configure the Identity Provider Redirector as follows:
Alias:GitLabDefault Identify Provider:gitlab
Test your Microcks configuration
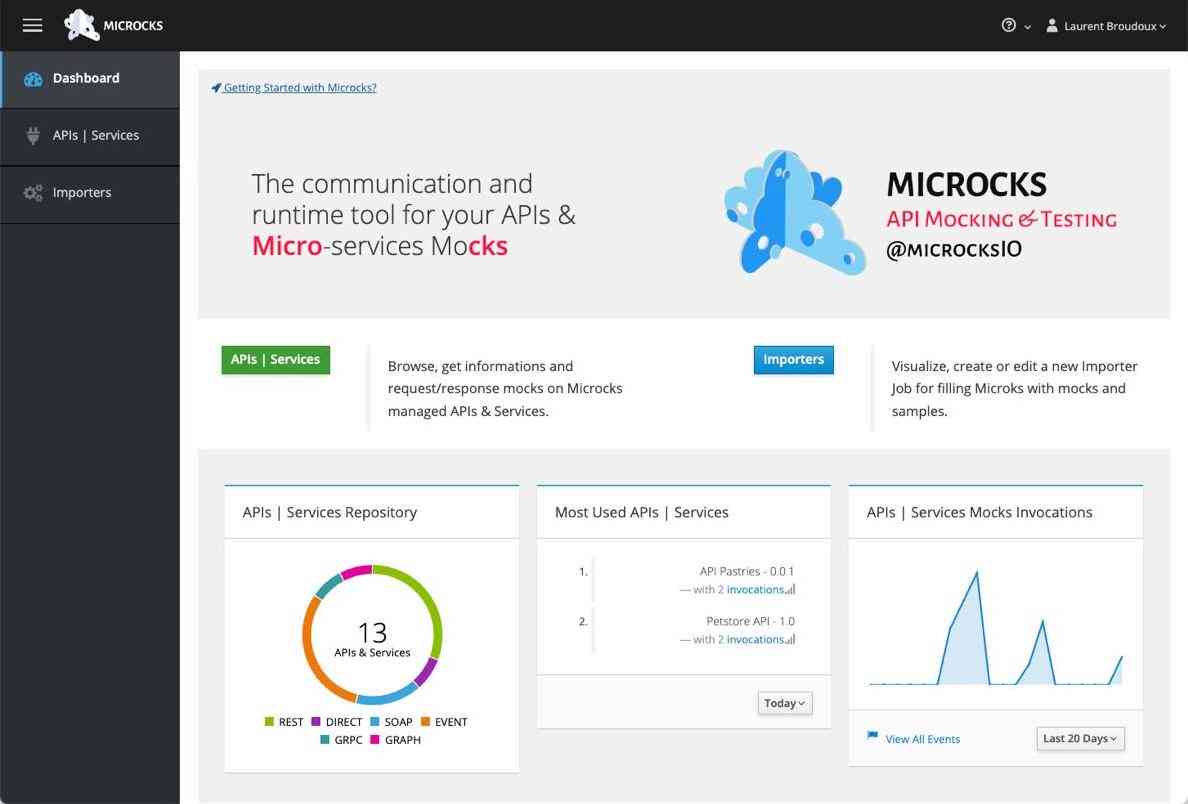
Now open the Microcks URL into your browser and you'll be directly redirected to the GitLab login page. Enter your GitLab credentials and you will be authenticated and redirected to Microcks.
What's next?
In upcoming blogs, we'll detail how GitLab can be used in the two major use cases for Microcks. We'll see how Microcks integrates with GitLab Git repositories to discover API specifications and produce simulations, and how to integrate Microcks conformance tests into your GitLab CI/CD pipelines.
Laurent Broudoux is a cloud-native architecture expert and enterprise integration problem lover. He has helped organizations in adopting distributed and cloud paradigms while capitalizing on their critical existing assets. He is the founder and lead developer of the Microcks.io open-source project: a Kubernetes-native tool for API mocking and testing. For this, he is using his 10+ years experience as an architect in financial services where he defined API transformation strategies, including governance and delivery process.
Madou Coulibaly is a senior solutions architect at GitLab.



