Learn how GitLab reduced incident resolution time from 30 days to 1 hour
Application security built into your software delivery flow
Application security built into your software delivery flow
Deliver secure software, faster with security testing in the same platform where teams and their AI agents already work.
Build secure products, with less security products.
Fewer tools, more secure software
Consolidate scanners like SAST, SCA, Secret Detection, and DAST into one intelligent orchestration platform — reducing cost, integration overhead, and time spent managing fragmented tools.
AppSec your developers will love
Security findings appear directly in merge requests and IDEs — no context switching, no new UIs, no separate systems, keeping developers in flow.
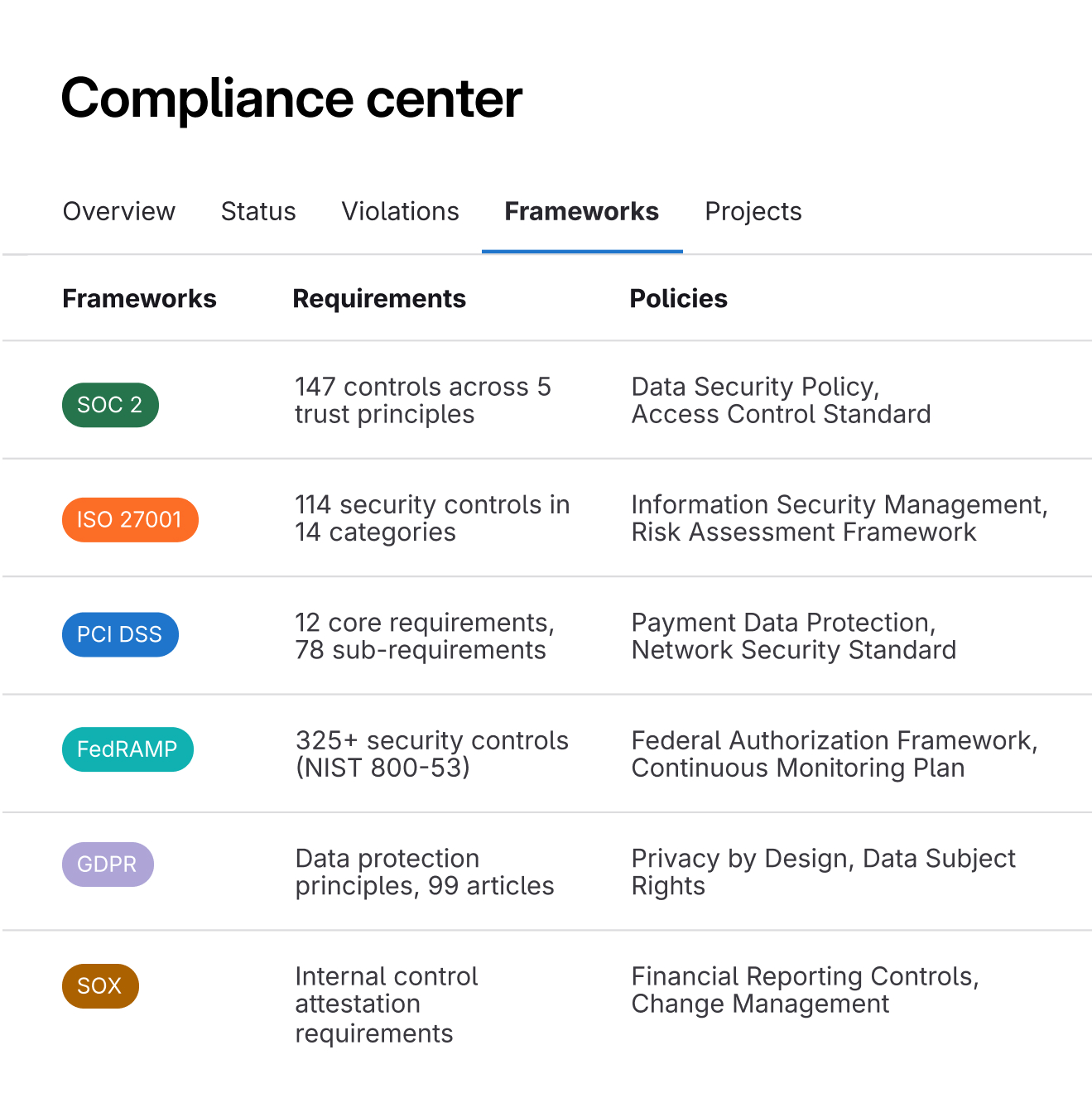
Software compliance? Check.
Apply controls for SOC 2, ISO 27001, and PCI DSS — and collect audit-ready evidence automatically in every pipeline.
Complete security coverage across the software development lifecycle
Find insecure code as it's written with guidance developers can act on directly in their merge requests.

Duo Vulnerability Explanation
Explains the vulnerability, how it can be exploited, and provides remediation guidance so teams and their AI agents can fix security issues faster, expand their abilities, and write more secure code.
Duo Vulnerability Resolution
Automatically creates a merge request with code changes to remediate the vulnerability, helping developers fix issues quickly without leaving their workflow.
If you want to secure your software, start where it’s built.
New security findings in production environments decreased by 20% to 25%*
New security findings in production environments decreased by 20% to 25%*
Built-in scans run on every push to detect insecure code during development.

Experience security scans running in the developer pipeline
Seamlessly integrate security scans into your CI/CD pipeline with intelligent orchestration. This ensures software teams and their AI agents receive early feedback on potential risks and vulnerabilities in their code, empowering you to ship more secure code faster.

Are you trading speed for security?
We've created a maturity framework based on our experience working with industry-leading customers. It offers prescriptive guidance on how to rapidly progress through three maturity stages.
Quiz takes 5 minutes or less

Proven results that scale
faster security scanning
 30%
30%of vulnerabilities were found earlier in the SDLC
 50%
50%faster vulnerability detection
 13x
13xfaster security scanning
 30%
30%of vulnerabilities were found earlier in the SDLC
 50%
50%faster vulnerability detection
 13x
13xfaster security scanning
 30%
30%of vulnerabilities were found earlier in the SDLC
 50%
50%faster vulnerability detection