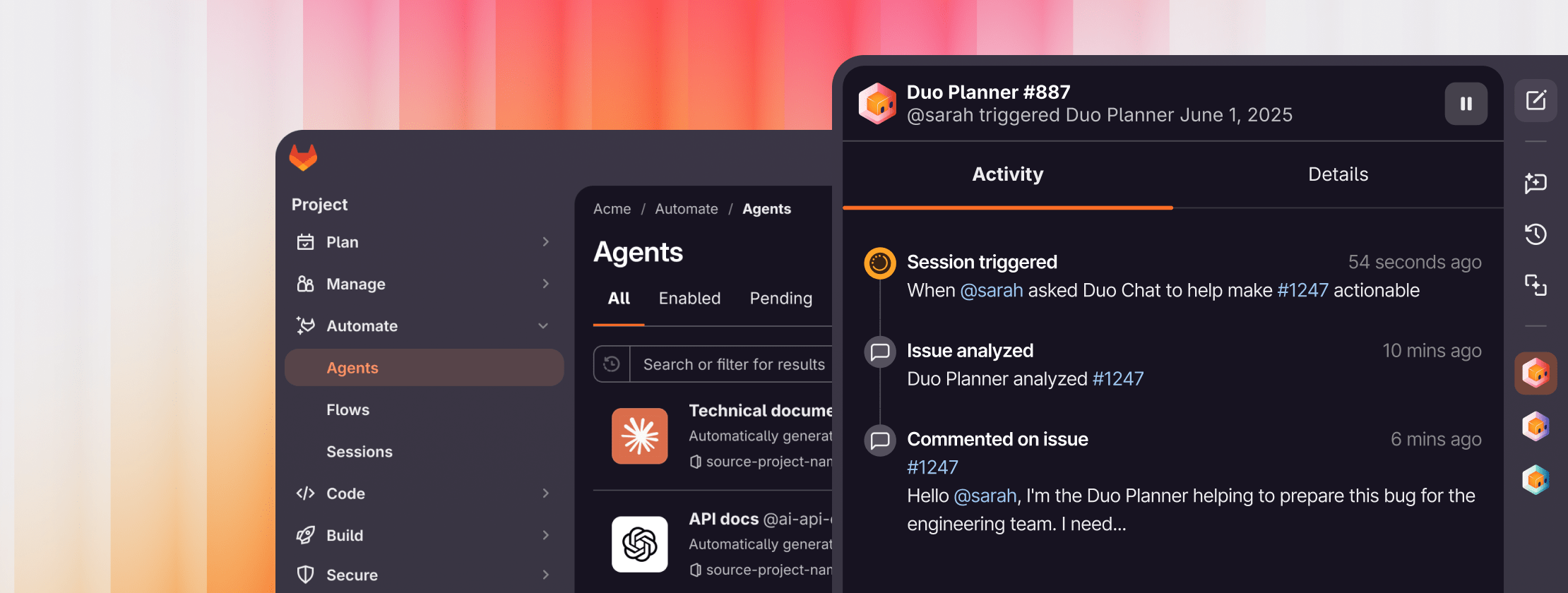
Are you just managing tools or shipping innovation?
We've created a maturity framework based on our experience working with industry-leading customers. It offers prescriptive guidance on how to rapidly progress through three maturity stages.
Quiz takes 5 minutes or less